Blockchain for digital content signature and integrity check
Few weeks ago I started a few posts to talk about #blockchain and its pratcital #applications. Here comes an idea of using it as an extension of #Digital #Signature for #Digital #Content and a mean of #governance #enforcement.
Photo by Patrick Lindenberg on Unsplash
Document signing
The main idea of the chain of blocks comes from the fact sets of data (“transactions”) are gathered and packed into “blocks” of data that are digitally signed together. This process called “mining a block” is perpetually performed as transactions are added to the registry. Once a block is “mined”, it is digitally signed and becomes immutable, then the digital signature of the signed block is put in the heading of the next block.
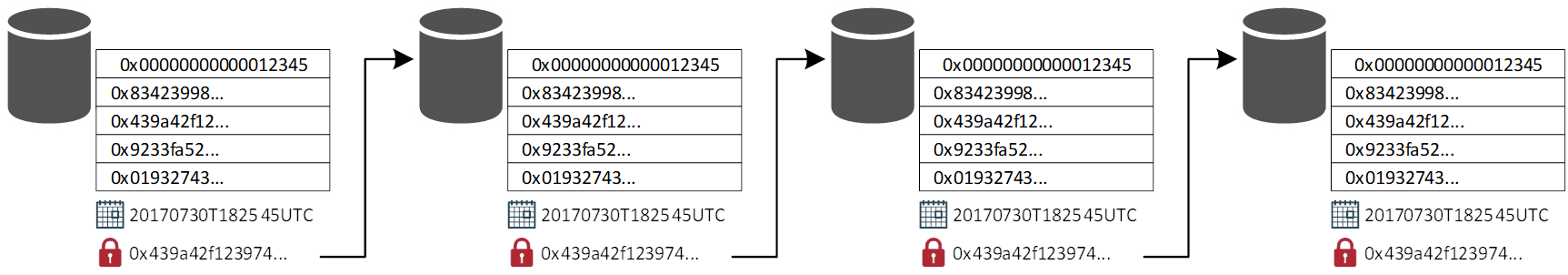
This allows us to have a block that is uniquely chained to the previous block by its digital signature. This happens from the beginning of the blockchain, the so called “genesis block” that is the beginning of the blockchain registry. This block is the only one that does not have a predecessor.
If you try to change a single bit in a block, a waterfall of failures will happen because all the digital signatures will fail.
Should a single bit of information change in the registry, all digital signatures will become invalid in the entire chain. If you change the digital signature in a single block, you should change it in the following block, and so on. Whereas this is something that could technically be done, the effort could be expensive for a few reasons:
- you would have to do this on the registries stored on no less than 51% of the total amount of nodes, and even then, it could not be enough (depending on the configuration and engine used)
- the system intrinsically has a timestamping system that keeps stores the time of the transaction when it is inserted in the system. If the dates are incoherent, they will be automatically rejected, and the registry will be marked as inconsistent.
The cost of such operation could become an expensive effort.
That makes a blockchain based registry extremely resilient to alterations of data.
Digital signatures of files have become an industry standard in 1996, the best example could be PGP (Pretty Good Privacy) and S/MIME (that strange thing that shows a “ribbon” in your e-mail client sometimes). I still don’t know why those systems didn’t become adopted in digital communications, but that’s another story.
A Digital Signature is a mathematical scheme that allows you to verify the integrity of an electronic document. It can be verified by any counterparty.
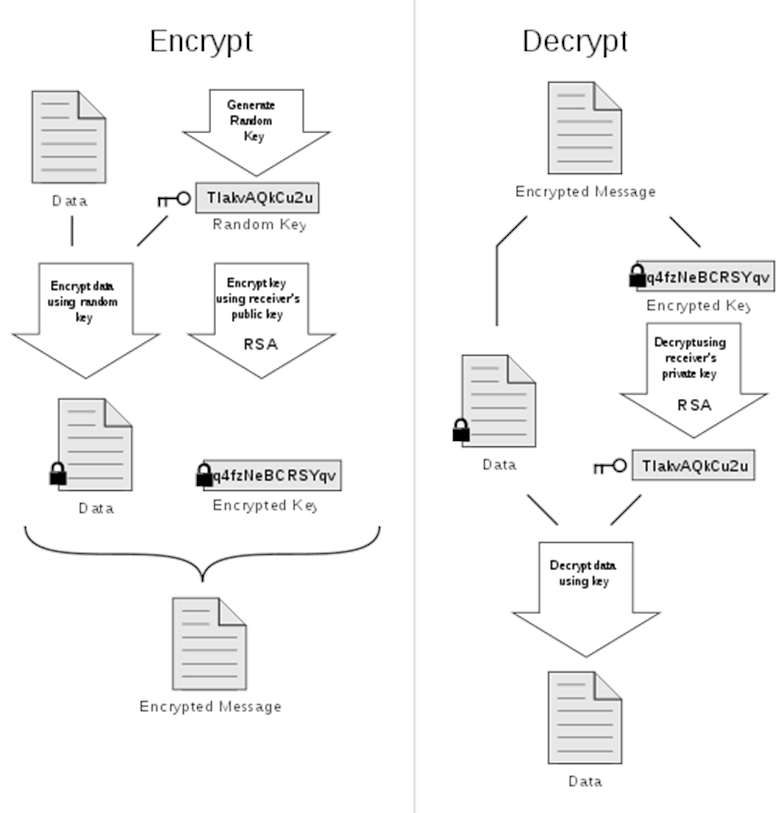
When we digitally sign a document, say a PDF document, we do the very same thing that Blockchain does when “mining” a block. Except the digital signature can be stripped off, or it can be removed from the file.
Digital document comes up in two flavours:
- embedded: the file contains its digital signature. A typical example is a PDF file digitally signed. It is self-sufficient and usually a PDF viewer recognises its signature and check its integrity.
- detached: this is usually what happens with PGP or when you find a “.p7b” file that is the digital signature of the file.
Depending on the verification software, Digital Signatures can even be crafted, as researchers found (more than once) in past (you can find a post about this problem in the Rights Chain blog).
What if we take a blockchain registry and use it to store digital signatures?
You obtain a reliable and resilient system to verify the integrity of the information that can be used by virtually any software or application without big efforts (I also wrote an essay about the use of “blockchain as an integration instrument” in mid-2018).
Why should I do that?
If you live in an environment with a strict governance, data integrity is be something you deal with. As cloud solutions becomes more popular within companies, “good faith” in your cloud service providers is not something you want to rely on. Well, unless it’s something mystical.
Let’s take a simple scenario I witnessed more than once.
You generate invoices for your customers with a software that does not support digital signing of PDF documents. These e-mails are sent via e-mail to all your customers.
One day your customer receives an email with attached a new invoice requesting a wire transfer on a “new bank account recently activated”.
If you think this scenario is not real enough, sorry but you’re wrong (feel free to see for this one).
Adding Digital Signature to your documents could be a good mean to prove your digital communication has not been compromised, but you could again fall in the problems mentioned above.
Integrating a signature verification process to any ERP software or process could also be very laborious.
You may consider using a registry based on Blockchain technology to store digital signatures of your digital documents instead.
With a blockchain registry you store every signed file with a simple API call that can be easily implemented into any application or programming language. You may even implement a Python script to sign the document as soon as it appears on the filesystem.
Since the Digital Signature is detached from the file but stored in an immutable registry, it can’t be counterfeit, removed or altered. Blockchain registries can be accessed using simple API commands that allows you to verify if the document’s integrity and owner.
Let’s bring this scenario even further.
Your documents being stored on an object storage outside the company. One day you discover your local storage is compromised and one or more data has been damaged and possibly lost.
Here things become interesting.
We are today used to have “faith” in systems and think that data virtually cannot be lost, that backup systems really backs up all the data and holds them upon the retention policy programmed. Or that our favourite cloud service provider does not lose file from their object storage when we move files from a short term to a long-term retention area.
Truth is, data can be lost, altered or damaged by either natural phenomenon (like hardware damages), intentional human intervention, or unintended effects like viruses or malware.
See how many times health systems were hit by some ransomware that disabled the access to vital information for days (ironically asking for ransom in Bitcoins… the technology created for the “good” of humanity being used against it).
We have two major scenarios here:
Data damage
Having an immutable registry will allow you to run an integrity check and spot all the damaged files in a glimpse. You can therefore recover the information from the backup system or the cloud storage.
Data loss
Do you really have all the data you assume to have?
I’ve been discussing this problem with a Customer worried the cloud copy did not contain all the data he uploaded.
Ask yourself the following questions:
- How do you check the existence of all your critical data on your local storage, backup or cloud service?
- Do you hold a registry of all the files and check them on a periodic basis?
- Are all the vital files present on the cloud and/or local storage?
A funny statement in IT Data Protection says that “a document becomes critical the exact moment it gets out of the backup retention policy”. Or is deleted. For good.
“a document becomes critical the exact moment it gets out of the backup retention policy”
Creating a registry of all vital digital data could be of great help to enforce governance.
Governance procedures are meant to help organisations and enterprises (but also small businesses) to make sure their workflows work as expected. Finding errors and correcting them is part of the process and shouldn’t be considered an issue. Well, unless it happens way too often.
Technology is a mean to enforce and simplify such processes.
Public or private?
That’s quite the religious dilemma.
Like I mentioned above, technology is a mean to enforce or simplify a process. Digital Data is something we have been using for the past three decades and nobody really treats is as an asset.
Are you annoyed? Delete your last corporate balance or governance report the day before an inspection or an audit.
Your data is… well… yours.
Your data, your processes, your governance and your enterprise. That sounds quite private to me.
I am neither a monk nor a priest, so using the most suitable technology for your needs is the only answer I might answer.
18/01/2020 00:00:00